The Rise of Synthetic Humans
2026-05-07
We have created machines that can imitate us.
This was, perhaps, inevitable. We have been trying to do it for a very long time. We have carved figures out of wood and stone. We have written stories about artificial beings who walk, speak, and occasionally develop inconvenient opinions. We have built dolls that blink and machines that answer questions. We have always been curious about what it would mean to make something in our own image, and then to see what happens next.
Now we are finding out.
At first, the imitations were clumsy. A slightly wrong voice. A face that looked almost right but not quite, like a painting hung slightly crooked. The illusion could be maintained for a moment or two, but not for long. One could tell.
Then, gradually, one could not.
A voice on the phone that sounds exactly like a colleague. A video clip that shows a person saying something they never said. An email that reads with the precise tone and phrasing of someone you know well enough to trust. Not identical, perhaps, but close enough that the difference becomes a matter of doubt rather than certainty.
We have crossed a line that is not marked on any map.
It is no longer simply a question of whether something is real or fake. It is a question of whether the distinction itself can be reliably made, and by whom.
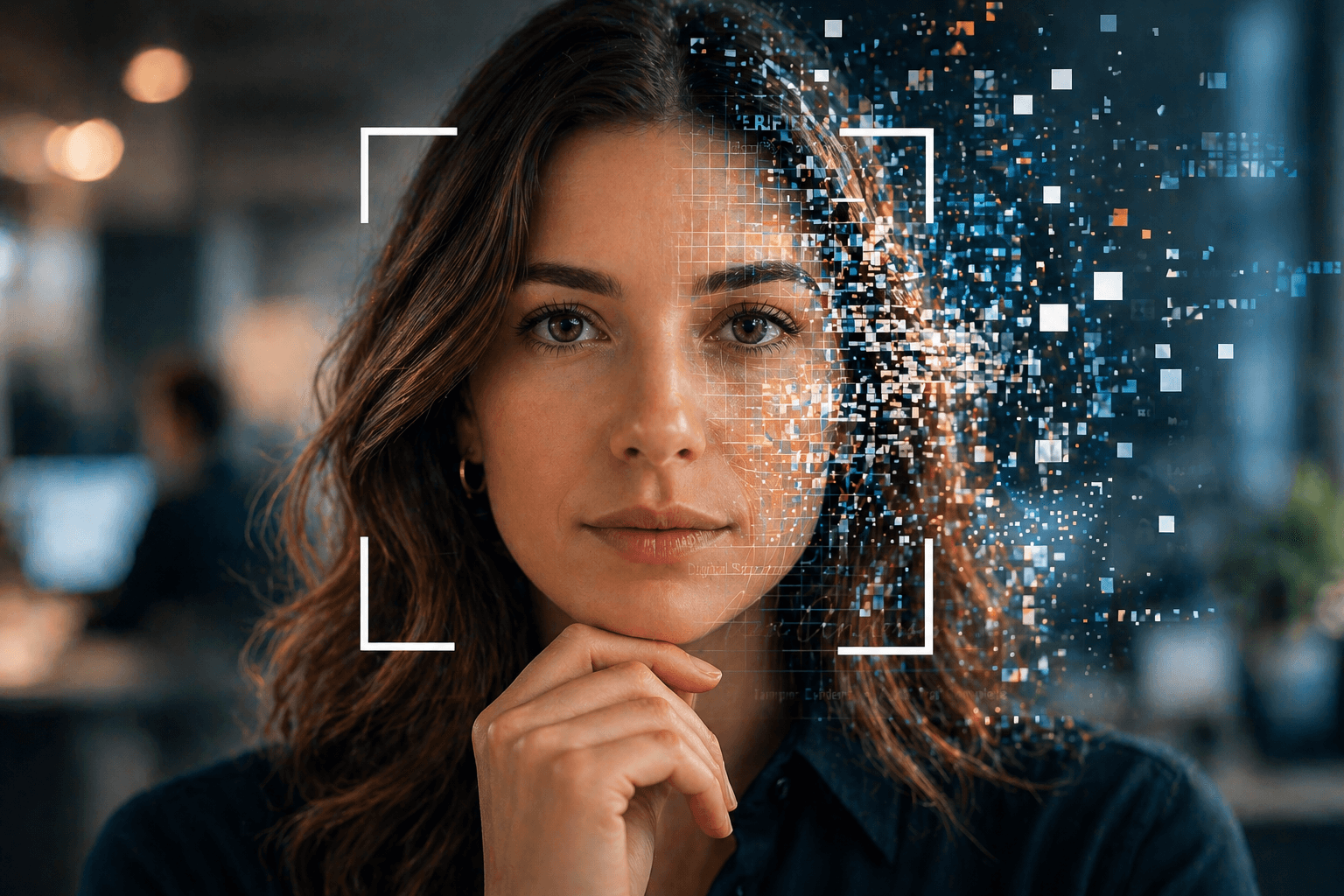
The phrase "synthetic human" may sound theatrical, but it is not entirely inaccurate. These systems do not merely produce images or text. They produce the outward signs of a person. A face. A voice. A style of communication. A set of habits that can be mimicked, repeated, and scaled.
They produce, in short, a presence.
Presence has always been a useful thing in human affairs. It is how we recognize one another. It is how we establish trust. It is how we decide, often quite quickly, whether the person in front of us is who they appear to be. We rely on it more than we realize.
What happens when presence can be manufactured.
One answer is that we begin to hesitate. The small, almost invisible moment of recognition becomes slightly longer. The certainty fades into probability. We are no longer entirely sure that the person speaking is the person they claim to be. We proceed anyway, because we must, but a question has been introduced.
And questions have a way of multiplying.
If a face can be generated, can it attend a meeting? If a voice can be cloned, can it give instructions? If a writing style can be replicated, can it authorize a transaction. If all of these things can occur, and increasingly they can, what becomes of the systems we have built on the assumption that identity is stable and observable.
Consider, for a moment, the humble act of signing a document.
Once, this required physical presence. A pen, a surface, a hand. The signature was not only a mark but an event. It occurred in a place, at a time, often in the presence of others. It could be witnessed. It could be challenged. It could be examined.
Then it became digital. Faster, easier, more convenient. A link, a click, a confirmation. The event was reduced to a gesture, the gesture to a record. The surrounding context faded into the background, and we told ourselves that the record would be enough.
It was, for a while.
But now we are introducing actors into this system that do not behave as we do. They do not tire. They do not hesitate. They do not experience doubt. They can imitate without understanding and persuade without intention. They can, if properly directed, perform the steps required to complete a process that was designed with human participants in mind.
One might ask whether the system notices the difference.
The system records that a link was clicked. It records that a document was accessed. It records that a signature was applied. It does not, in its simplest form, distinguish between a human hand and a synthetic one, between a person acting with intent and a process executing instructions.
It is doing exactly what it was designed to do.
The difficulty is that the world around it has changed.
This is not to say that synthetic humans, if we may continue to call them that, are malicious. They are tools. They do what they are asked to do, within the limits of their design. The risk lies not in their intentions, but in their capabilities, and in the assumptions we continue to make about how those capabilities will be used.
We have, in effect, introduced a new kind of participant into our systems without fully reconsidering the rules of participation.
The question, then, is not whether these systems will improve. They will. The question is what we do in response.
Do we continue to rely on signals that can be imitated. Do we accept a growing level of uncertainty as the cost of convenience. Or do we begin to design processes that take this new reality into account.
Some approaches suggest themselves.
If identity can be imitated, then identity must be verified in ways that are harder to replicate. If actions can be performed without intent, then intent must be captured more explicitly. If presence can be simulated, then presence must be observed, recorded, and linked to something that resists easy duplication.
This may involve additional steps. It may require a shift in how we think about what a signature is. It may move us away from the idea of a signature as a single moment and toward the idea of a signature as an event with context, evidence, and traceable identity.
It is a modest adjustment, conceptually speaking. It is also a significant one.
We are not the first to encounter this problem, though the scale is new. Throughout history, whenever a method of establishing identity became widely used, it eventually became widely imitated. Seals were forged. Signatures were copied. Documents were altered. Each time, new methods of verification emerged in response.
We are, perhaps, in the early stages of such a response.
Synthetic humans, if we wish to call them that, are unlikely to disappear. They will become more convincing, more accessible, and more integrated into everyday systems. They will assist us, entertain us, and occasionally mislead us, whether by design or by accident.
The systems that depend on identity will need to adapt.
So the next time a document appears, inviting you to click, it may be worth asking a slightly different question than the one we have been asking.
Not simply, "Is this ready to sign?"
But rather, "Who, exactly, is doing the signing?"
And whether, when it matters, that question can be answered with something more substantial than a very convincing imitation.